Need to remove htaccess WordPress Infection?
The .htaccess (short for Hypertext Access) is characterized as a design record utilized on web servers solely running on Apache Web Server programming.
This record as a rule includes an arrangement of orders essentially like the standard Apache web server setup documents.
By and large, these orders are key-esteem pair orders indicating on the off chance that a design ought to be on or off, however they can be more mind boggling. The area of the record is normally in the site’s root envelope, yet that said it very well may be in different areas also.
As and when the .htaccess record WordPress is set in a catalog, which is thusly stacked through the Apache web server, then, at that point, the .htaccess document is recognized and performed by Apache web server programming.
A portion of the highlights of the .htaccess record incorporate the capacity to secret phrase safeguard organizers, boycott clients or permit clients utilizing IP addresses, handicap catalog postings, divert clients to another page or registry naturally, make and utilize custom blunder pages, alter how documents with specific augmentations are used, or even utilize an alternate document as the list record by determining the record expansion or explicit document.
These .htaccess records can be utilized to make changes to the setup of Apache Web Server programming to empower/impair additional usefulness and highlights that Apache Web Server brings to the table.
These offices mostly involve fundamental divert usefulness, for example – in the event that you go over a 404 File Not Found blunder, or for further developed capacities like picture hotlink counteraction and content secret phrase insurance.
How .htaccess is used for exploitation by hackers?
Aggressors have been utilizing .htaccess for a long while now. Whether the assailants need to divert web crawlers or stow away malware, their best option is this document.
Plus, they likewise utilize this document for different reasons, for example, – infusing content, conceal indirect accesses, or adjusting php.ini values, and so on.
htaccess have a few assaults which can be utilized to sidestep some security elements or catalog limitations and so on the server .
For instance – on the off chance that you have an upload,php on server ,yet, you can’t transfer a shell straightforwardly or in a roundabout way .
You can for the most part sidestep those channels by transferring a .htaccess rather than shell .png , shell .php, shell. jpg and so on . Your transferred htaccess record will supplant the one as of now existing and you can sort out the rest .
Presently, the inquiry emerges why assailants over and again utilize a .htaccess document?
Here are the key justifications for why aggressors use .htaccess document so frequently –
This, right off the bat, is a secret document; attributable to this explanation, some site proprietors may not track down in their FTP clients.
Besides, being a strong record, making modifications to the web server and PHP conduct is made simpler. This is one of the key reasons .htaccess assault isn’t effectively discernible and difficult to tidy up.
Cleaning infected .htaccess file injected into all server folder!
There is a very common infection that hackers love to use on WordPress where they will inject an infected .htaccess file to every single folder within a Hosting account.
This is a complete nightmare from the website owners point of view because manually removing each of these files could take an enormous amount of time depending on how many folders are on the server.
The good news is that with a nice handy shell command you can remove all of these infected .htaccess files in less than one minute.
Please take a look at the steps below to walk you through this process.
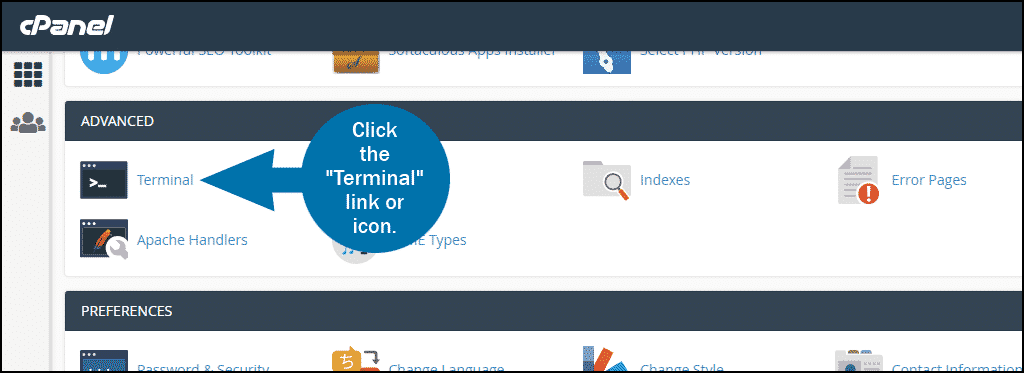
The information below is dependent on having a cPanel hosting environment or any hosting environment that allows for terminal access.
STEP #1 Fire Up Your Server Terminal
Since we will be running a server shall command we will need to get access to the server terminal.
Depending on which hosting platform you have, the steps to get access to this area may be different than what is below.
In the example below we are inside of a cPanel environment and simply clicking on the terminal area.
STEP #2 Run Shell Command to Remove all .htaccess Files
Once the show terminal has been opened and running there is a command that you will enter which will search and find all of the .htaccess files within the server and remove them.
In the images below you will see the terminal command window and the shell command that needs to run inside of this window which you can copy and paste and hit enter to run this command.
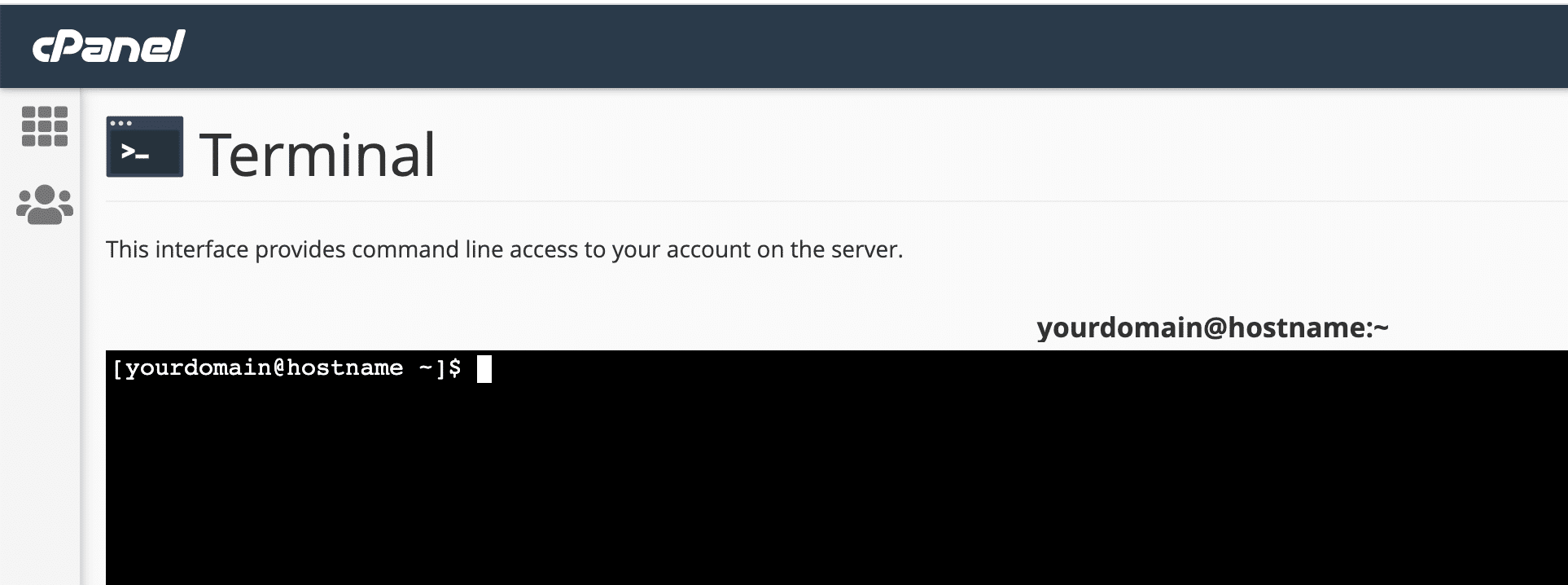
Below is the shell terminal command.
find . -name ".htaccess" -exec rm -rf {} ;STEP #3 Replace Needed .htaccess Files
Once you have run the shell command every single .htaccess file on the entire server will be deleted.
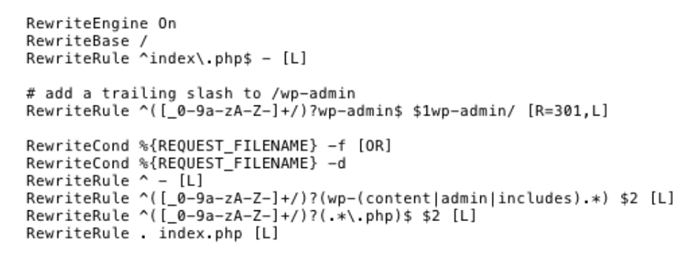
There is a required .htaccess file for each WordPress installation in order for it to function properly.
Because of the shell command that you ran the good ones have been deleted also.
You will need to reinstate the .htaccess file that each WordPress installation on the server needs.
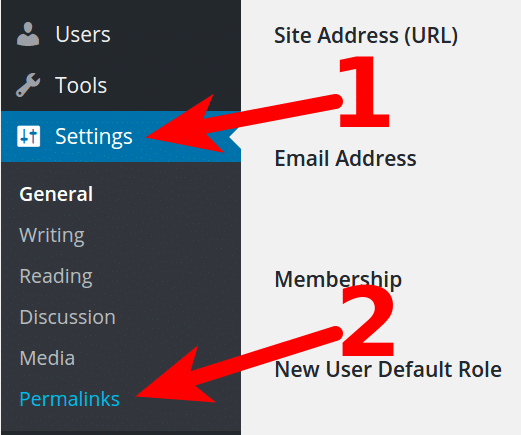
The easiest way to do this is to login to your WordPress administrative area and navigate over to your permalinks section under settings and simply re-save them.
IN CONCLUSION – Remove htaccess WordPress Infection
We hope that this post was helpful and reacting quickly to a server full of infected .htaccess files.
If you have any questions about the steps or this entire process feel free to comment below.












My wordpress now dont open…
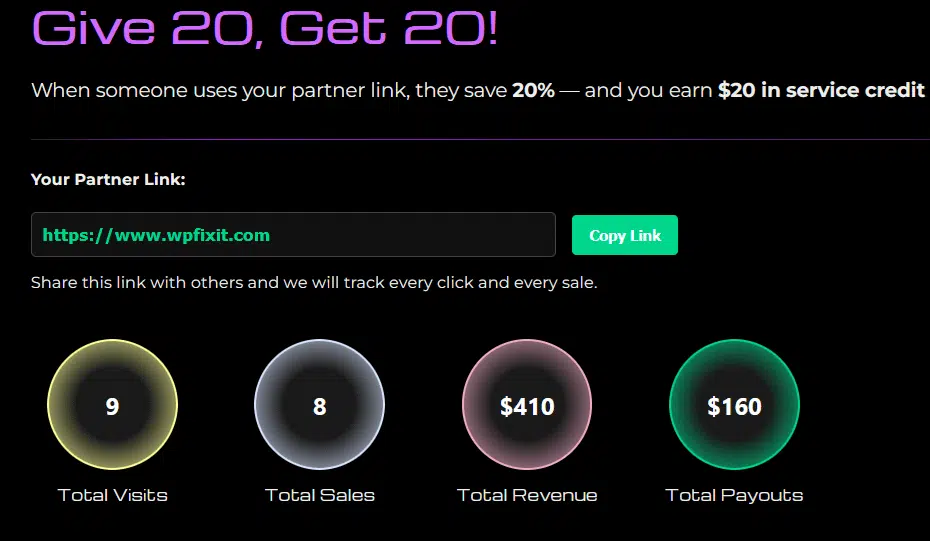
The service to get this fixed for you quickly is our Site Fix service. We have an agent ready to do the work right now. The direct link to this service is at https://www.wpfixit.com/fast-wordpress-support-service/
how do i access the terminal in bluehost to remove htaccess files. I’ve been dealing with this malware issue for over a month and i cant get to a solution as bluehost file manager doesnt have terminal in tit
Our Infection Removal service can get your site cleaned and secured. We have an agent ready to do the work right now. See full details at https://www.wpfixit.com/wordpress-infection-removal-service/
I really appreciate you kind gesture in putting up such a kind of article.
So how do I go about removing this infection.
Thanks.
Hello
If you need help with this you can purchase the service at https://www.wpfixit.com/remove-wordpress-malware-and-infections/